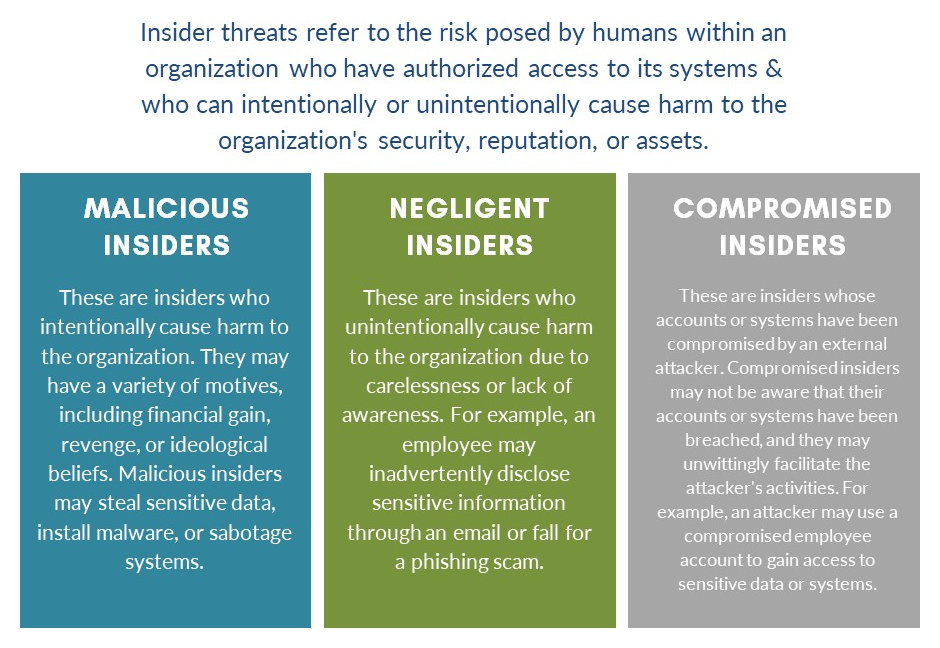
Insider threats can take many forms, including employees who misuse their access privileges for personal gain, intentionally or unintentionally disclose sensitive information, or engage in other malicious activities such as stealing data, installing malware, or sabotaging systems.
Insider threats are often difficult to detect and prevent because they involve individuals who already have legitimate access to the organization’s systems and data. To mitigate this risk, organizations implement various security measures such as access controls, monitoring and auditing, security awareness training, and incident response plans.

Recent Comments